-
About
- About Listly
- Community & Support
- Howto
- Chrome Extension
- Bookmarklet
- WordPress Plugin
- Listly Premium
- Privacy
- Terms
- DMCA Copyright
- © 2010-2024 Boomy Labs

 John Gruber
John Gruber
Listly by John Gruber
What you'll learn: Everything you need to know to pass the MS-500: Microsoft 365 Security Administration.

Get Certified in MS-500 Microsoft 365 Security Administration

Welcome to the MS-500 course on GitBit! In this course, you'll learn everything you need to know to pass the MS-500: Microsoft 365 Security Administration. You'll also learn everything you need to know to secure your Office 365 tenant. Throughout this course, we'll be doing a ton of lectures and a ton of hands-on. For a hands-on experience, we'll be using a free Microsoft 365 tenant.
We can start learning how to secure Microsoft 365 we will need a test tenant. A tenant where we can implement whatever you want and test things out before implementing them in production. A place where we can perform hands-on learning in a live environment without affecting production. Fortunately, we can set up a Microsoft 365 tenant for free to try out. You only need a free email address, such as gmail.com, outlook.com, or yahoo.com, and a phone number.
Microsoft 365 management is broken down into multiple admin centers. An admin center is a website used to manage part of the tenant. For example, there's an Exchange Online admin center that can help you manage the email portion of your Microsoft 365 tenant. Another SharePoint Online admin center to help manage the SharePoint Online part of your tenant.
Here's a list of all the Microsoft 365 admin centers you may need.
Creating users in Microsoft 365 is easy. Follow our guide to get started.
So let's talk quickly about creating users in Microsoft 365. Every user in your organization that requires a mailbox or admin role will be required to have a user account. The easiest way to add a user account is by creating a single user account in Microsoft 365.
How to connect to all Microsoft 365 services through PowerShell
PowerShell is a command-line + a scripting language combined. It's a powerful tool that can be used to automate actions on your computer as well as actions in Microsoft 365. But it doesn't manage Microsoft 365 out of the box. You first have to extend it which can be done using modules.
All the places you can assign admin roles in Microsoft 365
Introduction to roles in Microsoft 365.
Instead of granting all your admins admin roles that they have all the time you can grant users just-in-time (JIT) administration. With JIT you can have your admins request the access they need. The access can be time-limited so the admin can request the permissions they require to perform a function and then those permissions will automatically disappear after a short while.
with OneDrive you can keep items on your local device and sync them to the cloud. That way your files are available while you don't have an internet connection...
New to Microsoft 365? Get a quick run-down of AD Connect!
Trouble managing on-premises users and Microsoft 365 users? Sync them with AD Connect.
Password management in Microsoft 365: protection and ease of use. Simple to configure and simple to manage.
Everything you need to know about protecting passwords to pass the MS-500
Did you know users may give malicious apps access to your Microsoft 365 tenant? Protect your organization from compromised enterprise apps.
Conditional access policies help organizations improve security and compliance. They are used to fine-tune and customize the authentication of your users in Microsoft 365. Let me explain.
There are 5 different ways to enable MFA in Microsoft 365. Learn which way is the best way in this guide.
Self-service password reset in Microsoft 365 is a great way to empower users and decrease call volume to your IT help desk.
Tired of resetting users' passwords for them? Allow your users to reset their AD passwords through Microsoft 365 without admin intervention. Setup Self-service password reset!
How to lock down your Microsoft 365 tenant from Microsoft engineers
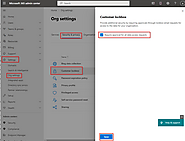
Customer Lockbox is a tool built into the Microsoft 365 tenant that locks out Microsoft engineers from accessing your tenant
Help prevent malicious data access. Use built-in controls to identify and manage risks inside your Microsoft 365 environment.
Implement artificially intelligent security using risk policies in Microsoft 365
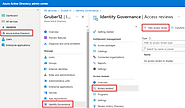
Too many groups for your IT team to manage? It's no problem with access review in Microsoft 365!
With Microsoft 365 access to your data is in motion unlike it has been before. Users can access your organization's data from personal devices and can even ...
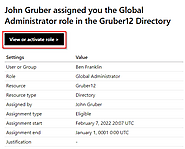
Everything you need to know about Just in time (JIT) admin roles in Microsoft 365
Just in time privileged access. Microsoft calls this Privileged Identity Management (PIM). With PIM users only have admin roles for a limited time. And befo...
Have Active Directory? Secure it now with Microsoft Defender for Identity
Microsoft Defender for Identity is designed to protect your on-premises Active Directory (AD) and Active Directory Federation Services (ADFS). Microsoft Defender for Identity can perform the following:
The meat and potatoes of Microsoft 365 security. The Microsoft Defender for Office 365 secures your entire Microsoft 365 environment.
Need to protect your Microsoft 365 tenant? Get started with Microsoft Defender for Office 365 today! Learn all the best practices and prepare for the MS-500!
Email is one of the most targeted attack vectors in your environment, and there are many moving pieces. There are spam and phishing attacks. And there isn't one size fits in terms of how they attack. They can use malware, attachments, and links. Anyway, if you're reading about the MS-500 then I'm sure you're aware of the security issues related to email. So without wasting a lot of time let's jump into the defenses.
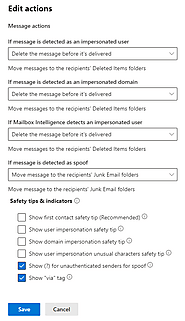
Has your organization been targeted by phishing attacks? Learn to protect yourself and your organization!
Blocking phishing attacks is a multi-part defense. Let's dig right into the settings and options to set up a defense.
Unless you're teaching them, your users will fall for phishing attacks. Learn how to simulate phishing attacks with Microsoft 365 today.
Phishing attacks are one of the most common ways an organization is attacked. According to the FBI, there were 241,342 complaints, with adjusted losses of o...
What is Microsoft Defender for Endpoint and how do I use it?
Unless you're protecting them, your user devices are the most vulnerable part of the organization. Learn how to protect them with Microsoft Defender for Endpoint.
The Microsoft Defender for Cloud Apps portal is a place where you can integrate Microsoft 365 and other third-party cloud apps to see what your users are us...
You definitely need a tool to catch shadow IT. Learn how Microsoft Defender for Cloud Apps can help protect you and your organization.
