-
About
- About Listly
- Community & Support
- Howto
- Chrome Extension
- Bookmarklet
- WordPress Plugin
- Listly Premium
- Privacy
- Terms
- DMCA Copyright
- © 2010-2024 Boomy Labs

Listly by Listly
.

My first Defcon was Defcon Three, held at the Tropicana Hotel in Las Vegas. The computer security conference scene was much, much smaller back then, but Defcon had already become THE security conference of the year. Since that time I've continued to regularly attend Defcon, and over the years I have collected some very fond memories of summer computer security conventions past.

Reputation Every Friday, we'll highlight the most important Cisco partner news and stories of the week, as well as point you to important, Cisco-related partner content you may have missed along the way. Here's what you might have missed this week: Off The Top This week Cisco unveiled details around the popular Value Incentive Program (VIP) 22.

Behind the Contours of the Contour Earlier this week, our colleagues at Cox took the wraps off a beauty of a next-new version of personalized television, branded "Contour." It's a continuation of its service extensions earlier this year into screens "beyond the TV," such as iPads, tablets, laptops, and smartphones.

Over the last several weeks, I've been posting a blog series around nine HIPAA network considerations. HIPAA Audits will continue The HIPAA Audit Protocol and NIST 800-66 are your best preparation Knowledge is a powerful weapon―know where your PHI is Ignorance is not bliss Risk Assessment drives your baseline Risk Management is continuous Security best practices are essential Breach discovery times: know your discovery tolerance Your business associate(s)must be tracked This week we focus on #5 - Risk Assessment drives your baseline.

Cisco Blog > Borderless Networks Is Your Branch Office Lean Enough? Many branch offices rely on Cisco ISR G2 (Integrated Services Router, Gen 2) as their IT platform. This router series delivers highly secure data, voice, video, and application services through a modular design.

According to a recent Cisco News article the Internet of Everything (IoE) is a multi-trillion dollar opportunity that incorporates data gathering, data processing, data analysis, data visualization, data optimization, data storage and retrieval, etc. Data is being generated at an exponential rate and with the IoE even more data will be generated.

DNS records are an attractive target for distributors of malware. By compromising the DNS servers for legitimate domains, attackers are able to redirect visitors to trusted domains to malicious servers under attacker control. DNS requests are served from dedicated servers that may service many thousands of domains.

Business mobility is driving better productivity, heightened customer experience, and harmonious work/life balance. It also offers freedom for knowledge workers beleaguered by accelerating demands on their time and talents. Indeed, workers themselves have taken much of the initiative toward business mobility.

Reputation Earlier this year, the number of connected devices reached the 10 billion mark, surpassing the world's human population, and experts expect that number to reach 50 billion over the next two years. This phenomenon, known as the Internet of Things (IoT), comprises a highly distributed model of connected objects, devices, and sensors that are used to communicate data.

Those of us who cover broadband frequently bemoan its two steps forward, one step back progress, and the idealists among us yearn for a "Sputnik" moment that will galvanize regulators and carriers alike to leap forward into the future. Will broadband have such a moment, and if so, what will it look like?

Cisco's support of the Russian Government's modernization agenda got a big step forward this month. We recently announced the official opening of the Cisco Experience Center at the Skolkovo HyperCube - part of an overall effort to further develop an innovation ecosystem in Russia.

Reputation In this week's episode of Engineers Unplugged, we send the marketer in to chat with the technologist. Steve Shah (@steveshah) quizzes Nisarg Shah (@nisargcisco) around the use cases for NetScaler including load balancing in the Application Driven Data Center. Less talk, more TLAs!

Cisco's Value Incentive Program (VIP) is in its 22 nd consecutive period and has more than ever to offer. Over the years we have invested billions of dollars into VIP and into you, our partners. For this launch period, we want you to take a fresh look at your VIP strategy to get the most from this incentive program.

Cloud platforms are an increasingly viable option for a growing set of enterprise and service provider workloads. A recent IDC report estimated that private cloud software, including hosted private cloud, represented 62% of IT spending in 2012. Cisco is a unique cloud provider because it delivers solutions for the two critical management bookends for your journey to the cloud.

One of the things I enjoy most in my role leading Product Management for Cisco's Customer Collaboration business is listening to our customers and partners to ensure we deliver products that meet their needs. Our focus on delivery and execution sets Cisco apart in the industry.

The focus of this post is on the upcoming PCI SSC North American Community Meeting which is being held September 24-26, 2013, at the Mandalay Bay Convention Center in Las Vegas, Nevada. The meeting spans two full days of knowledge sharing, networking, and learning, which includes Keynote presentations from industry experts, PCI case studies, and Technical sessions.
Over the last several years, the role of an enterprise workforce has evolved from a select few mobile-enabled employees to a robust, global network equipped with advanced capabilities at their fingertips. As this workforce grows and evolves, how can enterprises, specifically their IT departments capitalize on opportunities available through mobility while meeting their ever-increasing workforce expectations?

Reputation On the heels of the Let's Chat! #Ciscosmt Series: Social Media for Events USTREAM panel discussion a couple of weeks ago, I wanted to share my recent experience with Cisco LIVE. I remember the late 90s when I started working in the tech sector.

Reputation It's interesting to think back to the times when a manufacturing job meant hard labor, a lack of automation and crowded plant floors. Flash forward to the manufacturers of today and the differences in productivity and efficiency are incredible.

I gotta be honest here. I not a big fan of many of our marketing programs here at Cisco. Well, really it's the launch vehicles that I think are too flowery and silly to be honest. I'm sure analyst clap their hands like ...

Cisco Blog > Digital and Social Engaging Teams in Social Media: Twitter Chat - August 20, 2013 #CiscoSMT Reputation This meter represents your reputation at a 100% scale based on your level of participation on the site.

Editor's Note: This blog post was co-written by Dr. Brendan O'Brien, who is authoring the post, and Dr. James Little, technical lead for CMX Analytics in Cisco's Wireless Networking Group. This year's CiscoLive! in Orlando with over 20000 visitors was selected as an ideal opportunity to test and prove CMX Analytics over a large venue with high volume usage.

Reputation During the last three years, the security research community has been having a lot of fun with SSL/TLS uncovering a few nifty attacks. First, in 2011, Juliano Rizzo and Thai Duong released the details about the BEAST attack on Transport Layer Security (TLS) at the ekoparty Security Conference in Buenos Aires, Argentina.

By Linda Horiuchi, senior manager, Australia and New Zealand PR Last week, Cisco hosted an event in Sydney, Australia, to discuss the Internet of Everything - What is it? Are there early examples of the Internet of Everything in Australia? What does Australia need to do to take advantage of the opportunities it offers?
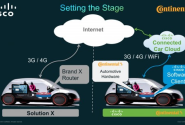
With Cisco's heritage in networking the enterprise, we understand how to create a secure, scalable and high performing networking framework - one that enables connectivity and new user experiences. In a nutshell, this has been the foundation for our efforts in connecting cars.
